

Phishing is a social engineering tactic that threat actors use to persuade individuals to provide sensitive information and/or take a desired action, such as clicking on a malicious link or opening a malicious attachment. Messages are typically designed to appeal to a recipient’s sense of fear, greed, duty, or curiosity.
Phishing in healthcare the number one cybersecurity threat to health systems of all sizes and types. It’s also is the number one cause of significant security incidents and the primary means by which threat actors gain access to systems and networks. The motives of threat actors vary, but often their targets are as follows: financial information, patient information, disruption of systems and networks, and/or pivot points to other systems/networks.
An attack is easy to set up and deploy. Now, since many individuals, companies and other entities have significant online digital footprints, it is relatively trivial for threat actors to glean valuable information about their intended victims. The cost and time involved in putting together a targeted campaign is fairly trivial. Phishing is an ideal way to obtain access to the inside of systems and networks, since the recipients of the messages typically have inside access.
Awareness of this threat needs to be top of mind, not only for information and technology staff, but also for all workforce members and others who have access to the organization’s systems and networks. Regular and frequent awareness training and education is recommended for everyone. Having a once a year briefing on this topic is not enough. These tactics always change and it is important for everyone to understand how the threat landscape is changing.
In light of the COVID-19 pandemic, many organizations are having to deal with more workforce members working from home or from otherwise remote locations. Healthcare organizations are making it a priority for systems, networks and other resources to be available on-demand. However, some organizations are failing to adequately protect the systems, networks and other resources. In other words, having too much availability essentially opens up the infrastructure to the world and threat actors only need to find one vulnerability to exploit.
The weakest link in any organization is the human factor. This is why this tactic is a significant threat and the attacks are so effective.
Many of the attacks are now COVID-19 themed and threat actors are following the news cycle to tailor the content. Attacks may be timed so that they are sent at the beginning of the day, end of the day, or during a time when the recipient may have a lot of meetings. Factors such as fatigue and/or distraction may lower a person’s ability to detect deception in a message. Attacks may also take advantage of the fact that many people are working remotely and they may not trust but verify by popping their head in a colleague’s office to confirm an unusual or odd request, e.g., wiring of money. Emails, websites, text messages (also known as SMiShing) and social media are common vectors for this attack.
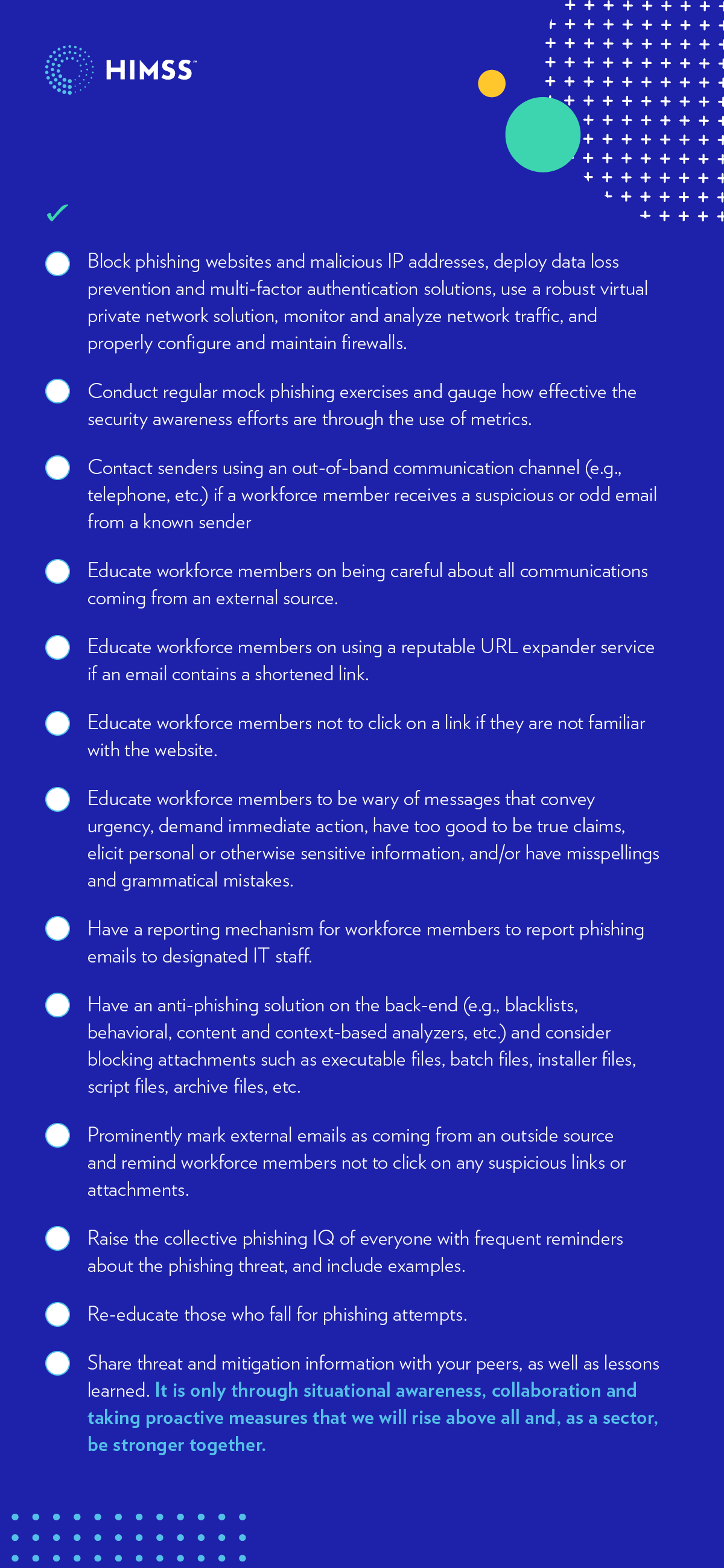
With the foregoing in mind, the following checklist—a non-exhaustive list of tips—may be useful in mitigating the threat of phishing in healthcare.
HIMSS Healthcare Cybersecurity Survey
Gain insights into the healthcare cybersecurity landscape based on feedback from industry professionals in our cybersecurity survey report.
Originally published August 25, 2020